 With the recent MS14-025 security patch Microsoft has removed the ability to configure passwords in Group Policy Preferences via the User Interface. However this update does not remove the password value from AD nor does it stop the value being applied to computers/users. So, if you have apply MS14-025 and you have also implemented another way of managing the local admin password (see my other post How to set the Local Administrator account to a Random Password ) the next thing to do is to remove all the passwords from AD so there is no traces left of the old insecure passwords.
With the recent MS14-025 security patch Microsoft has removed the ability to configure passwords in Group Policy Preferences via the User Interface. However this update does not remove the password value from AD nor does it stop the value being applied to computers/users. So, if you have apply MS14-025 and you have also implemented another way of managing the local admin password (see my other post How to set the Local Administrator account to a Random Password ) the next thing to do is to remove all the passwords from AD so there is no traces left of the old insecure passwords.
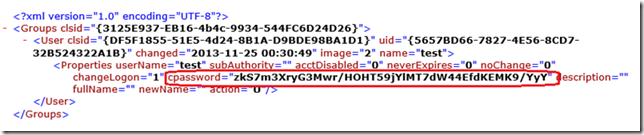
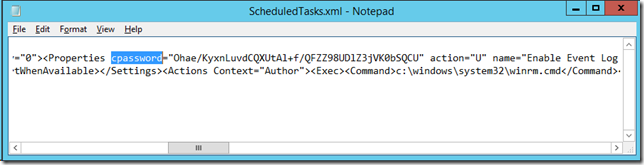
Side Note: These passwords in AD that Group Policy preferences user are also know as cPasswords because that is the name of field that is used to save the password value (see below)
How insecure is the cPassword field? See my post Why Passwords in Group Policy Preference are VERY BAD. Then remember that even you have deployed MS14-025 and you are managing password via other mean’s you might still have passwords in your organisation that have not be changed, so these passwords might still be valid on some computers.
So along with the password reset PowerShell script released in the MS14-025 Microsoft they also provide a script that allows you to identify the polices. Below I go thought and show how you can run this script and how you can purge the scourged of cPasswords in your organisation.
First of all go to http://support.microsoft.com/kb/2962486 and copy the Get-SettingsWithCPassword.ps1 script from the page and save that as a file called “Get-SettingsWithCPassword.ps1†on the computer you are going to run the script.
Note: You will need to run “Set-ExecutionPolicy -ExecutionPolicy Unrestricted†on the computer to run this script as it is not signed. Be sure to not leave your computer in this state as it does reduce the security of your system.
Then open a PowerShell command prompt from any workstation, preferably one that has read access to all the GPO’s which is most accounts by default.
Warning: Depending on the size of your System Volume and how fast your network and domain controllers are this can take a VERY LONG time (Hours).
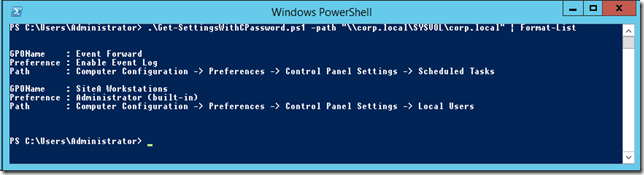
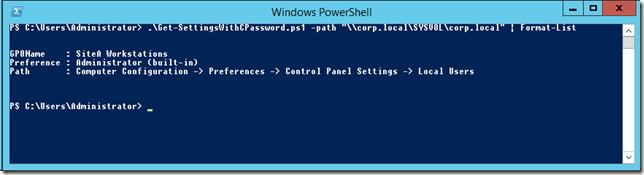
Then run the following command (replacing the highlighted values with your own DNS domain name):
.\Get-SettingsWithCPassword.ps1 –path “\\corp.local\SYSVOL\corp.local†| Format-List
As you can see it has now listed the Group Policy Objects name and path to the setting in your domain that have the cPassword value configured.
TIP: You may want to run this script on your environment straight away on your environment to see how pervasive the use of the cPassword value is in your environment. (I am betting a lot).
Removing cPasswords the easy way
The easiest thing to do to remove these values would be to simply go in an delete the relevant Group Policy Preferences settings or the Group Policy Object. This will delete all the files that contain the cPassword value from SYSVOL thus purging the value.
Removing cPasswords the hard way
But this Group Policy Preference might be part of a complicated Group Policy Object or other Group Policy Preferences settings so you *might* want to just remove the cpassword value surgically.
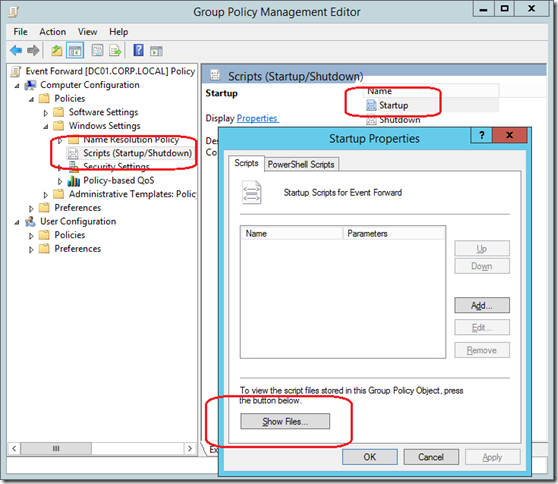
To do this open up the Group Policy Management Console and edit the affect GPO so that we can go to the relevant file in the SYSVOL for that GPO. Then navigate to the Computer Configuration (or user) > Policies > Windows Settings > Scripts (Startup/Shutdonw) then click on the “Startup†script and then click on the “Show Files…†button.
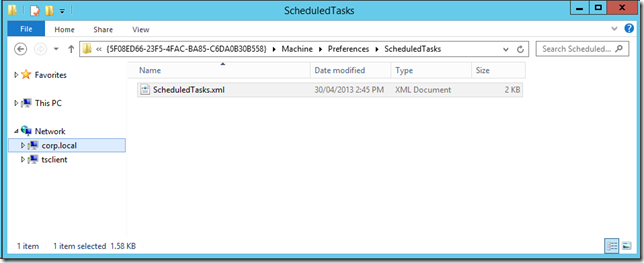
This will open up Windows Explorer somewhat close to the folder that has the cPassword value stored. You will need to go up the “Machine†(or User) folder and then open up the “Preferences†folder.
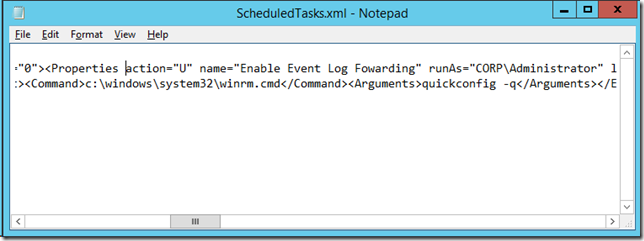
Now open Notepad.exe as an administrator and open the XML files in that location (in our example it is ScheduledTasks.xml).Now search for the name “cpassword†and it will jump to the location that the cPassword is stored.
Note: It is important to open up notepad as administrator (or with permission to edit the GPO) otherwise you will not be able to save the file.
Warning: Be sure that you have replaced the functionality of this Group Policy Preferences using another method as this will break the functionality of the setting.
Now delete the entire cpassword field from the XML and save the XML file.
You can run the script again to confirm that the cpassword filed is removed from AD.
So I expect this is the last in the series of post about cPassword value in Active Directory. Hopefully by now you are fully aware of the issues with passwords with Group Policy Preferences (see Why Passwords in Group Policy Preference are VERY BAD) and that you have prepped your environment (see How to enable WinRM via Group Policy) to enable password management via the means (see How to set the Local Administrator account to a Random Password). You then applied MS14-025 to all your computers (see Group Policy Preferences Password Behaviour Change – MS14-025) and have been trying to identify and limit the use of the cPassword values using this post.
So how many cPasswords do you have in your environment? Please shout out the number in the comments below.






Blog: How to remove cPassword values from Active Directory http://t.co/mz4P13xU6n
RT @alanburchill: Blog: How to remove cPassword values from Active Directory http://t.co/mz4P13xU6n
How to remove cPassword values from Active Directory: http://t.co/T8rgKwbZEp
RT @alanburchill: Blog: How to remove cPassword values from Active Directory http://t.co/mz4P13xU6n
Cómo eliminar valores cPassword de Active Directory. #SharePoint VÃa: @alanburchill http://t.co/cWL8FDqEFs
How to remove cPassword values from Active Directory: http://t.co/VtmFHqn581
RT @ldap389: How to remove cPassword values from Active Directory: http://t.co/VtmFHqn581
RT @alanburchill: Blog: How to remove cPassword values from Active Directory http://t.co/mz4P13xU6n
Thanks for the summary, Alan.
Contrary to what you’ve written, it’s a commonly-known fact in PowerShell circles that the PowerShell execution policy has no bearing on the security of your system.
It’s easily bypassed, and all of PowerShell’s functionality comes from the underlying .NET framework and depends on whatever the user has permission to do. Have a read of the comments on this blog post if you’re curious as to how it’s bypassed: http://obscuresecurity.blogspot.com.au/2011/08/powershell-executionpolicy.html
Cheers,
Daniel
How to use this in conjunction with GPO Scheduled tasks?
There is no alternative for scheduled tasks…. you are going to have to configure that on a per server basis
Why not just restrict user access to the xml file containing the CPassword value? If it is a machine side preference “authenticated users” are not required to have access for it to run. Remove them from the security and add the required machine group (i.e. “domain computers”, “domain controllers”, etc.). This would prevent regular users from being able to read the CPassword value in the first place.
Would this not work?
Hello Alan,
I have applied LAPS to our environment. I see that the generated password on attribute but the password won’t work. Please help.