Recent Posts
Edge Chromium IE Mode Now Works
In the past few weeks there has been a lot of post about the new Enterprise features coming with the new Edge Chromium version of the browser. Unfortunately the main feature that enterprises were waiting for did not work… until today.
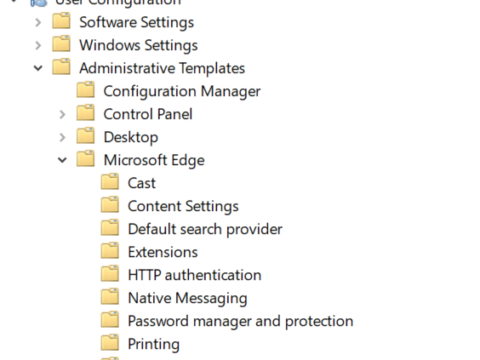
Edge Chromium Group Policy Settings
Microsoft Edge Chromium Group Policy setting have been released for testing, take a look at how to download the new settings and what settings are still missing.
Security Baseline template for Windows 1903
Microsoft has released the latest security template for Windows version (Windows 10 and Windows Server) 1903. These templates contain updated guidance and recommendations as to what setting should or should not be configured to your domain joined PC. The security template is actually just a bunch of reports, documents, GPO backups and tools that are consolidated in a s single…
New and Fixed Group Policy Setting with Windows 10 KB4490481
New and fixed Group Policy Setting with Windows 10 KB4490481
Security Baseline Recommendation for Windows 10 1809
After its initial release and then withdrawal of Windows 10 1809 update due to a number of potential data loss issues, Microsoft has now again released the OS to wide scale deployment. As a such a number of other release have now come from Microsoft, namely the Security Baseline templates GPO’s, documentation with recommended guidance and scripts to help secure…
New Microsoft Edge MDM and Group Policy Settings
Microsoft just documented the new policy setting for Microsoft Edge. These settings can be configured via both MDM and Group Policy. To get use the policy settings you need to be running at least Windows 10Â Preview build 17718. Then you can then install Group Policy management Console (now part of Core OS) and trial the new Policy settings. For a…
Microsoft releases V2 of the Windows 1803 Administrative Templates Pack
Back in May 2018 Microsoft released the Windows 1803 ADMX/ADML file pack . This was par for the course as with each release of Windows Microsoft would also release a new version of the ADMX/ADML Administrative Templates Pack. However, the release in May could cause an error in GPMC if you had previously had an old version of the SerachOCR.ADMX…
Group Policy Hotfix for Defender Mitigation Options Error
Just a quick note that Microsoft has recently release a hot fix KB4338819 that fixes and issue with the Mitigation option. This is a Windows Defender setting that can be found under the Administrative Templates>Computers>System>Mitigation Options setting. The fix is described as: Addresses an issue that may cause the Mitigation Options Group Policy client-side extension to fail during GPO processing….