Edge Chromium IE Mode Now Works
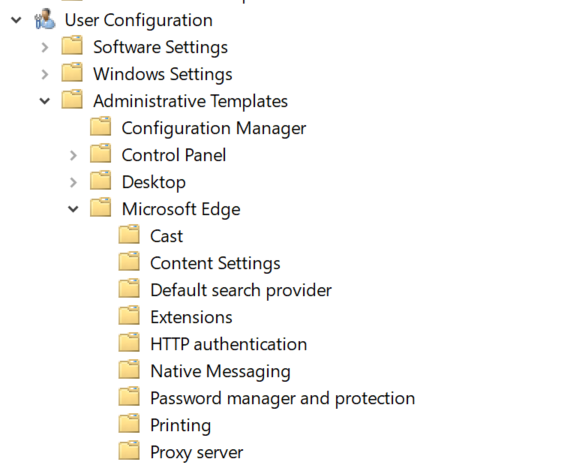
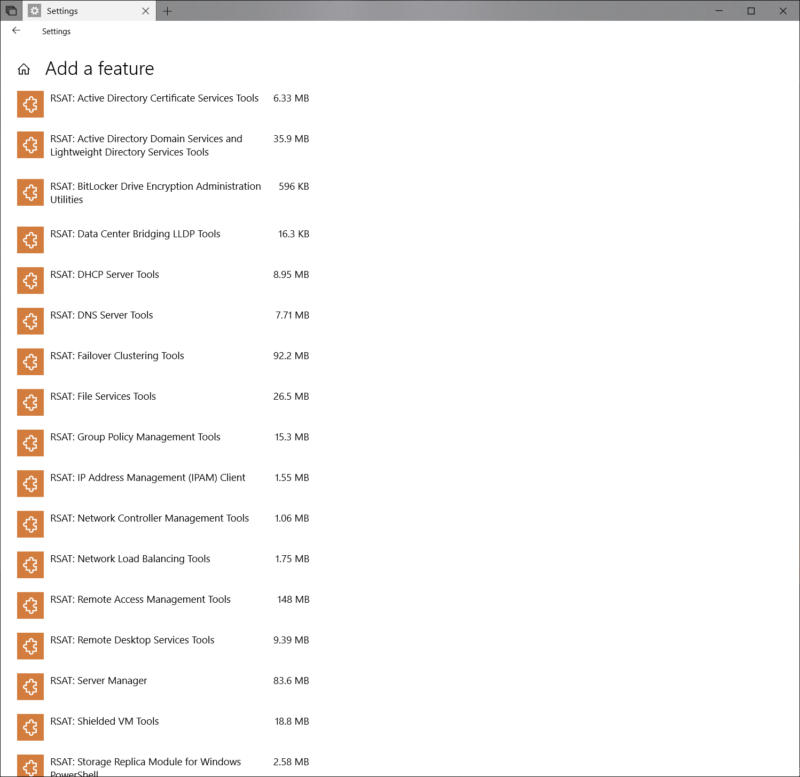
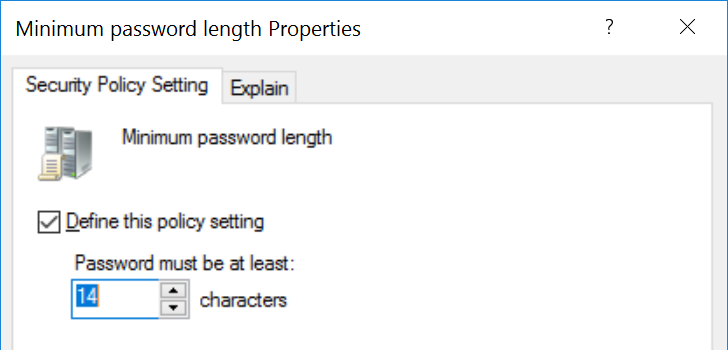
In the past few weeks there has been a lot of post about the new Enterprise features coming with the new Edge Chromium version of the browser. Unfortunately the main feature that enterprises were waiting for did not work... until today. One of the k...
Continue Reading →