Running the add-QADPermission PowerShell command
Step 1. To run the add-QADPermissions PowerShell command click on the PowerShell shortcut (that blue one in the taskbar if you are running 2008/R2).
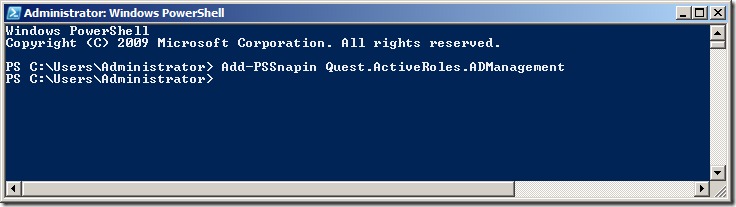
Step 2. Run the command the following command to load the Quest PowerShell commands.
Add-PSSnapin Quest.ActiveRoles.ADManagement
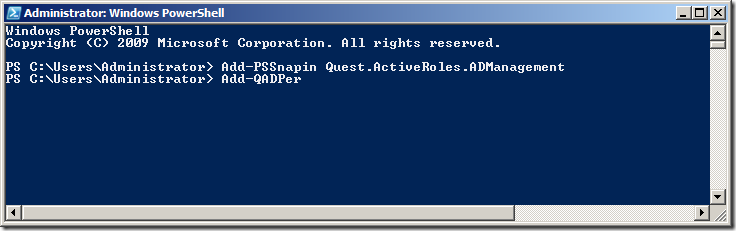
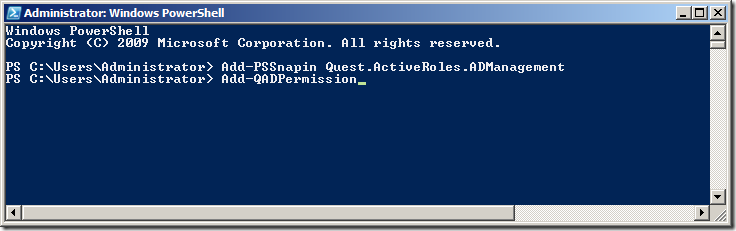
Step 3. To test that the new PSSnapin is loaded type “add-qadper†and then press the “Tab†key to complete the command.
This should auto-complete the command to “Add-QADPermissionâ€
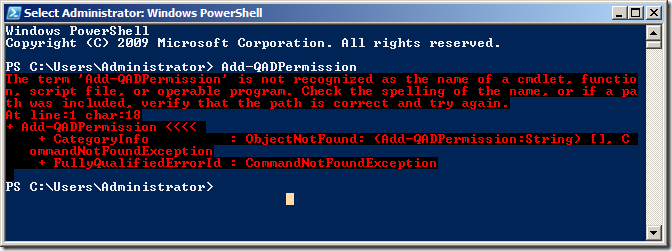
REMEMBER: Every time you launch a new PowerShell window you are going to need to run “Add-PSSnapin Quest.ActiveRoles.ADManagement†to load to load the Quest PowerShell Snapin’s otherwise you will see a message like the image below.
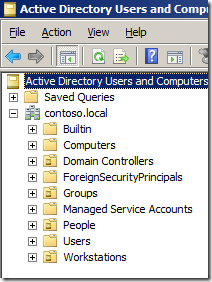
Now that we have verified that the new Quest AD PowerShell commands lets take a look at the command that will replicate some of the common tasks in the “Delegation of Control Wizardâ€. In our example environment that we have an AD with three top level OU’s called “People†“Groups†and “Workstations†(see below). These OU only contain the same type of objects that match the name of the OU (e.g. “People†contains User AD Objects) but it is possible to delegate all the permissions to the same single OU if it contains objects of multiple types (e.g. user,computers and groups).
Delegating Create, delete and manage user accounts permissions using add-QADPermission
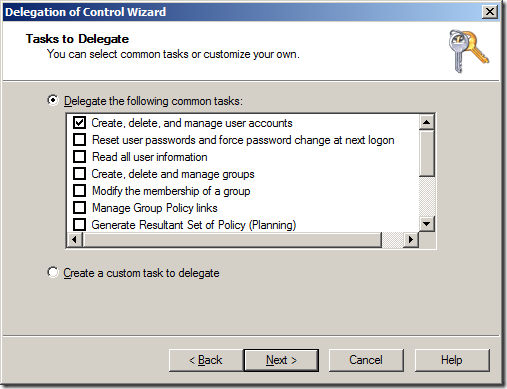
To delegate the same permission as the “Create, delete, and mange user accounts†(effectively Full Control) option in the “Delegation of Control Wizard†(see below) you need to delegate two permissions to the OU.
- Allow access to all the properties of the user objects
- Create / Delete permission of the user object
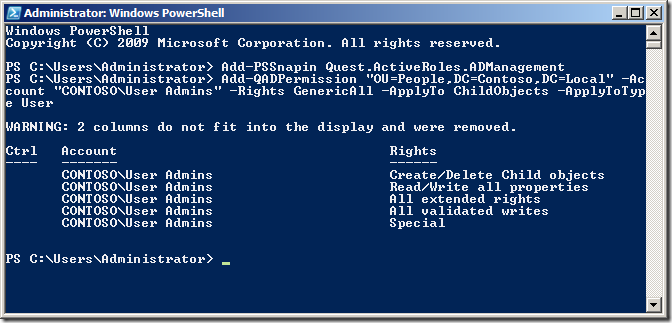
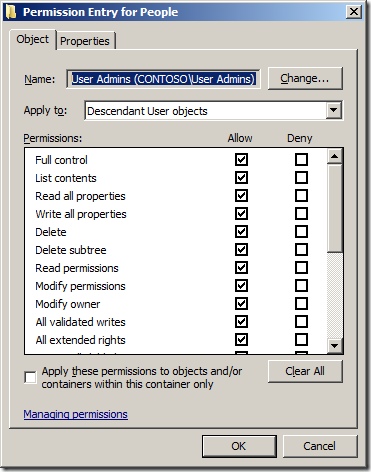
The first command will delegate Allow access to all the properties to the group called “User Admins†to all User objects in the OU with the distinguished name of “OU=People,DC=Contoso,DC=Localâ€.
Add-QADPermission “OU=People,DC=Contoso,DC=Local†–Account “CONTOSO\User Admins†-Rights GenericAll -ApplyTo ChildObjects -ApplyToType User
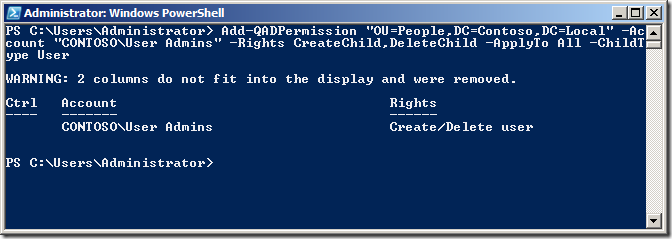
The second command will delegate Create / Delete permission for the User objects to the same OU for the same group.
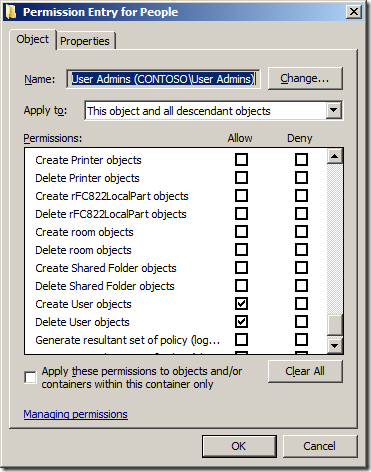
Add-QADPermission “OU=People,DC=Contoso,DC=Local†-Account “CONTOSO\User Admins†-Rights CreateChild,DeleteChild -ApplyTo All -ChildType User
Now we can check the security on the People OU in Active Directory Users and Computer to verify the permission has been added correctly.
Note: See how we have used the “-ApplyTo ChildObjects†parameter and the “ApplyTo All†to ensure that these permission will inherit to all objects in this OU and sub-OU’s.
If the OU that you want to give the same Full Control permission to a Computers or Groups AD Object type all you need to do is change the -ApplyToType and -ChildType parameter to “computer†or “group†(See examples below)
Example delegation Create, delete and manage (a.k.a. Full Control) Groups permissions using add-QADPermission
Add-QADPermission “OU=Workstations,DC=Contoso,DC=Local†–Account “CONTOSO\Workstations Admins†-Rights GenericAll -ApplyTo ChildObjects -ApplyToType Computer
Add-QADPermission “OU=Workstations,DC=Contoso,DC=Local†-Account “CONTOSO\Workstations Admins†-Rights CreateChild,DeleteChild -ApplyTo All -ChildType Computer
Example delegation Create, delete and manage (a.k.a. Full Control) Computers permissions using add-QADPermission
Add-QADPermission “OU=Groups,DC=Contoso,DC=Local†–Account “CONTOSO\Groups Admins†-Rights GenericAll -ApplyTo ChildObjects -ApplyToType Group
Add-QADPermission “OU=Groups,DC=Contoso,DC=Local†-Account “CONTOSO\Groups Admins†-Rights CreateChild,DeleteChild -ApplyTo All -ChildType Group





Blog Post: How to delegate AD permission to Organisational Units using the PowerShell command Add-QADPermission http://bit.ly/dcXL9O
How to delegate AD permission to OUs using PowerShell. http://t.co/OGMAKjv via @grouppolicy_biz Good stuff that I might have to "borrow"
RT @alanburchill: Blog Post: How to delegate AD permission to Organisational Units using the PowerShell command Add-QADPermission http://bit.ly/dcXL9O
How to delegate AD permission to Organisational Units using the PowerShell command Add-QADPermission http://t.co/7RHgwWP
How to delegate AD permission to Organisational Units using the PowerShell command Add-QADPermission
Is your organization sensational? Is that why you spell it organisational?
You spell Organisation with an S in Australia…
Allan;
When I try to use the Add-QADPermission commandlet (following your example above) in a test environment I get the following error:
Add-QADPermission : The search filter is invalid.
At C:\WindowsPowerShell\test-it.ps1:33 char:18
+ Add-QADPermission <<<< -Identity "OU=New-OU,dc=XXX,dc=XXX=dc=XX,dc=XX" -Account "-XXXX Delegation of Authority\Security Role Groups\Role-Adm-Account-Management" -Rights GenericAll -ApplyTo ChildObjects -ApplyToType Group
+ CategoryInfo : NotSpecified: (:) [Add-QADPermission], LdapException
+ FullyQualifiedErrorId : System.DirectoryServices.Protocols.LdapException,Quest.ActiveRoles.ArsPowerShellSnapIn.Cmdlets.AddPermi
ssionCmdlet
I have tried both with and without the '-identity' parameter specified and with the input string as above and also in a variable.
I haven't run into any similar problems running other commandlets from the snapin but this one has me stumped. Any suggestions as to what I've got wrong.
Not sure if it is just how you typed it but… -Account “-XXXX Delegation of Authority\Security Role Groups\Role-Adm-Account-Management” appears to be wrong… there should not be more than one “\” in the group name…
Okay, now I get.
WARNING: Can’t lookup account for identity: ‘XXX.XXX.XX.XX\Role-Adm-Account-Management’
WARNING: No valid accounts specified. Searching permissions for all accounts.
WARNING: Can’t lookup object for identity: OU=New-OU,dc=XXX,dc=XXX=dc=XX,dc=XX
I’m running my testing at (this point) as Domain Admin in the test environment so why can’t I look up the identity?
Looks like you are not using a valid Netbios domain name… should only be 15 characters with no dots
Your post helped me a lot, but had some issues with delegating Reset Password Permission
Here is what I found out
The command: Add-QADPermission “OU=People,DC=Contoso,DC=Local†-Account “CONTOSO\User Operators†-ExtendedRight User-Change-Password -ApplyTo ChildObjects -ApplyToType User
need to be changed to
Add-QADPermission “OU=People,DC=Contoso,DC=Local†-Account “CONTOSO\User Operators†-ExtendedRight User-Force-Change-Password -ApplyTo ChildObjects -ApplyToType User
User-Change-Password
Permits changing password on user account.
User-Force-Change-Password
Permits reseting password on user account.
Reference: http://technet.microsoft.com/en-us/library/ff405676.aspx
If you use the delegation Wizard to delegate the Reset Password permission, you’ll find out the a get-qadpermission, returns RIGHTS: Reset Password, not Change Password
Hi to all, it’s in fact a pleasant for me
to go to see this site, it consists of valuable Information.
My homepage; pdf books
I can’t see a way to delegate control to an OR, i can easily do it for group.
These powershell extensions appear to no longer free since the company changed to One-Identity.
Instead its a 30 day trial.