Update: Microsoft have now released the patch to the .lnk vulnerability MS10-046: Vulnerability in Windows Shell could allow remote code execution . If you have previously deployed the workaround using this article then it is now time to reverse the change you made by simple jumping to Removing the KB2286198 Workaround via Group Policy section and following the instructions. Needless to say this is a particular bad security issue and that you should be deploying this patch to all the computers in your environment ASAP. You have been Warned!!!
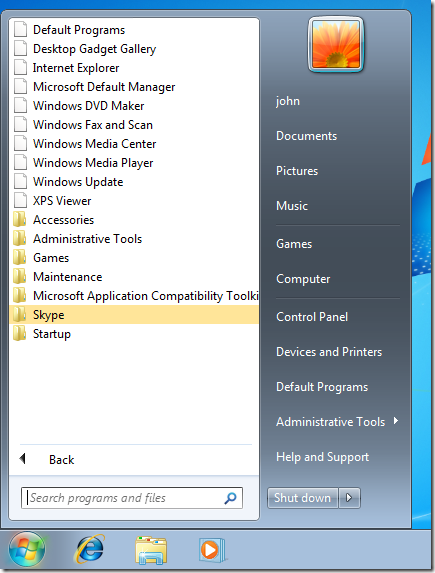
There is currently a Microsoft Security Advisory KB2286198 out that affects all copies of Windows about a security issues with displaying icons on shortcuts via non-local drives (e.g. Removable, Network and WebDav folders). The security advisory lists the workaround to the issues that effectively disables displaying all shortcuts. While this is not exactly a prettiest workaround (see image below) it does prevent you from being vulnerable to the security exploit.
There is a Microsoft Fix It for the issues if you just want to apply this workaround to a handful of computers but below I will show how you can apply the same workaround to all your domain computers using Group Policy.
KB2286198 Workaround via Group Policy Instructions
First we are going to create a policy that we can use at a later stage to restore the icon handler. The value that we are
Step 1. Edit a Group Policy Object that applies to all the computers you want to apply the workaround
Step 2. Navigate to Computer Configuration > Preferences > Windows Settings > Registry and in the menu click on Action > New > Registry Item
Step 4. Change the Hive to “HKEY_CLASSES_ROOT†then type “lnkfile\shellex\IconHandler†in the Key Path then tick Default and type “{00021401-0000-0000-C000-000000000046}†in the “Value Data†field and then click OK
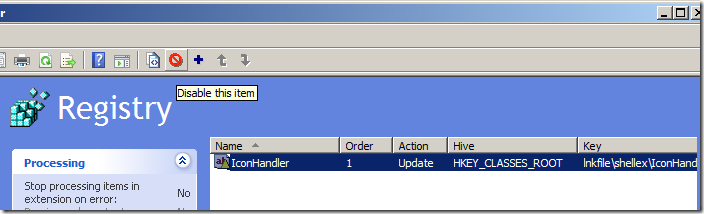
We now want to disable this entry as we are going to use to to restore the Icon Handler once you the patch for this issue is out.
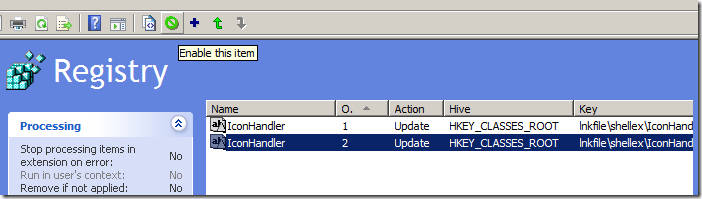
Step 5. Click on the IconHandler item in the right hand column and then click “Disable this item†(Red Circle) in the toolbar.
Now we create the entry that disables the Icon Handler…
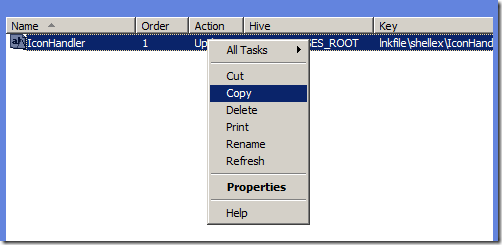
Step 6. Right click on the IconHandler registry item you just created and click “Copyâ€
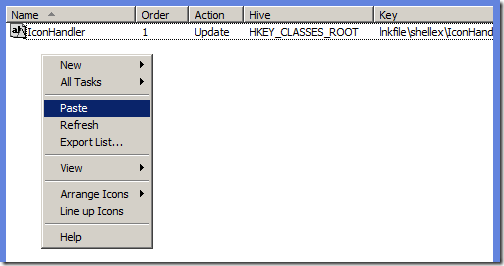
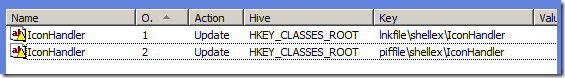
Step 7. Right click somewhere in the blank in the right column and click “Pasteâ€
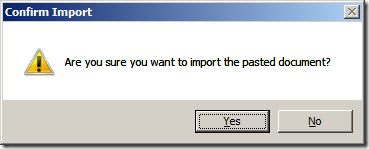
Step 8. Click Yes
Step 9. Click on the second IconHandler registry item and click “Enable this item†(Green Circle) in the toolbar.
Step 10. Double click on the second IconHandler registry item and clear the “Value Data†field then click Ok.
Step 11. Now select and copy both IconHandler 1 & 2 and paste them again into a blank area (see step 6,7 & 8).
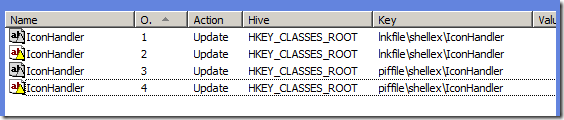
Step 12. Double click on IconHandler 3 & 4 and change the “lnkfile†in the Key Path to “piffile†(should now look like below image).
Now we are going to disable the WebClient Service that is the second part of this workaround…
Step 13. In the same GPO navigate to Computer Configuration > Preferences > Control Panel Settings > Services and in the menu Action > New > Service
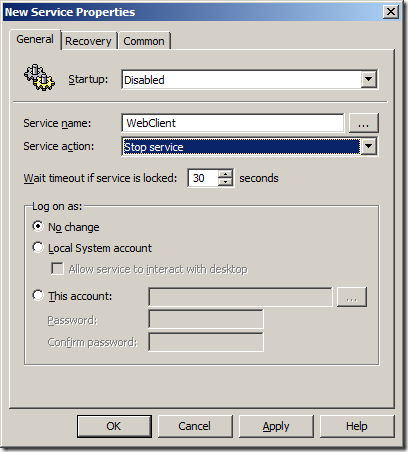
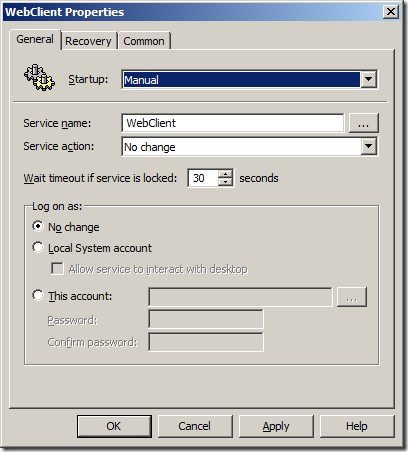
Step 14. Change the Startup value to “Disabled†and type “WebClient†in the Service Name text field then change the Service Action to “Stop Service†and click OK.
Done…
The workaround will now push out to all you workstations and become affective on the next reboot (see image below).
Removing the KB2286198 Workaround via Group Policy
Step 1. In the GPO you set this up in navigate back to Computer Configuration > Preferences > Windows Settings > Registry and delete enabled registry entries (probably the second and fourth) and then click on the remaining two registry entries and click on Enable this item in the toolbar (see image below).
Step 2. In the same GPO navigate to Computer Configuration > Preferences > Control Panel Settings > Services and double click on the WebClient service item and change the Startup to “Manual" and the Service Action to “No change†then click OK.
Hopefully this will keep you secure until Microsoft release a patch for this security issue. As always implement these fixes at your own risk and I make no guarantees that these workaround will necessarily work in your environment.
Further References
- http://securitygarden.blogspot.com/2010/07/fix-it-released-for-security-advisory.html
- http://securitygarden.blogspot.com/2010/08/critical-out-of-band-update-released.html
- http://support.microsoft.com/kb/2286198
- http://www.microsoft.com/technet/security/advisory/2286198.mspx
- http://www.microsoft.com/technet/security/bulletin/ms10-046.mspx






doesnt work still have icons
I found that the icons only dissapeared from the All Programs menu in the start menu…. I am assuming that as long as the reigstry key locations are being cleared and the WebClient service is stopped you should be safe as that is what the MS article says…. Of course that menas we trust the MS article is correct.
Update: How to workaround KB2286198/MS10-046 .lnk Icon security issues with Group Policy http://bit.ly/aqNdnz