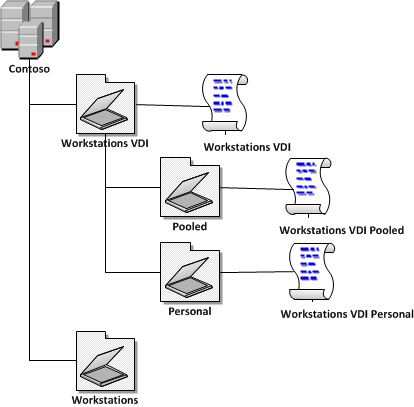
Organisational Unit Structure for VDI
The Organisational Unit Structure for VDI computers will probably look something like the image below. This method keeps the OU structure relatively flat but it also means that you need to duplicate some setting in your normal workstations GPO’s. I think this is an acceptable trade-off as these polices will have Loopback enabled so you can apply user specific setting to these computers (more on this later). I also think if you made the VDI OU a sub-OU of your Workstations OU it would be very difficult to troubleshoot issues with conflicted settings. This configuration would also unnecessarily give your normal workstation administrators control over the VDI computers that you normally want to control a LOT more tightly.
In your environment your VDI OU probably won’t be directly under the Top Level of the domain but this should still give you a template that you can use in any part of your AD. If you have read my previous blog posts Best Practice: Active Directory Structure Guidelines – Part 1 and Best Practice: Group Policy Design Guidelines – Part 2 you may recognize that this design is similar to how I split Laptops and Desktops OU’s (You may also notice that I have also kept with a naming convention that adheres to these two blog posts as well.). The reason why this looks similar is that just as workstations can be classified as either Desktops or Laptops so can VDI workstations be classified as Pooled and Personal, hence the similar design. This also means that for this structure to work ALL VDI computer accounts MUST be in either the Pooled or Personal OU. This would therefore make it invalid to have a compute account directly in the VDI OU.
Here is a description of the three main group policy objects that are applied in this configuration:
- Workstations VDI – This GPO will have all the setting that need to be applied to all your VDI workstations.
- Workstations VDI Pooled – This GPO will only have all the setting applied specific to your Pooled VDI workstations.
- Workstations VDI Personal – This GPO will only have the setting applied specific to your Personal VDI workstations.
Loopback for VDI
There are various user setting you may want to apply to your users when they logon to the VDI computer. Just as with Remote Desktop Service the use of the User Group policy loopback processing mode is the setting that allows you to apply these users setting.
Further on in this post I discuss many user setting that you might want to configure however if you don’t have any users setting configured in your VDI Group Policy Objects then there will be no need to enabled loopback.
Initial Computer Configuration for VDI (Native Only)
Note: This following configuration setting will only need to be applied if you are using a native VDI Implementation without third-party VDI software.
It is important that you configure the workstation for VDI as described it this guide Deploying Personal Virtual Desktops by Using Remote Desktop Web Access Step-by-Step Guide . Thankfully there is a PowerShell script that can do all the configuration changes for your VDI workstations image that you can download from http://go.microsoft.com/fwlink/?LinkId=184804 . However scripts are only a one time configuration and I like to re-enforce these changes with Group Policy where possible to ensure the configuration does not vary. Doing this also makes it easier to discover what changes have been made by running a GPResult report on the computer. Another advantage of having Group Policy makes all these changes is that all the configuration changes are automatically applied to your workstations when they are built making the process quicker and less likely to be forgotten.
Warning: Any additional setting via Group Policy could cause extra overhead so you many want to only be selective as to what initial computer setting you apply via Group Policy. For that reason you may want to consider running the PowerShell configuration script as a one time “Immediate†task on the computer via Group Policy instead of configuring all these changes individually.
If you chose to use Group Policy instead of a script (good on you) to setup your VID environment then make the following configuration change in the “Workstations VDI†Group Policy Object.
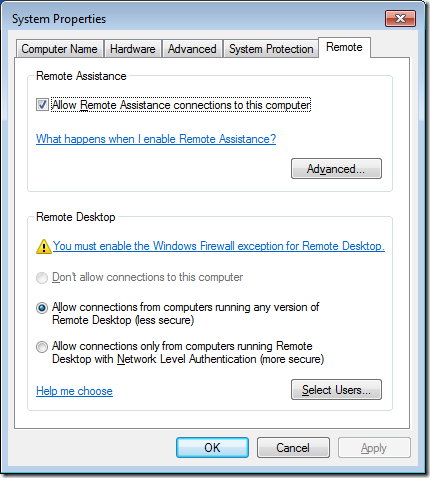
Enable Remote Desktop
You can enabled Remote Desktop using the Allow users to connect remotely using Remote Desktop Services setting. This will change the configuration of your computer to allow Remote Desktop Connections to the VDI workstation. However as you can see from the image below this does not open up the require firewall port (3389) to allow an incoming RDP connection.
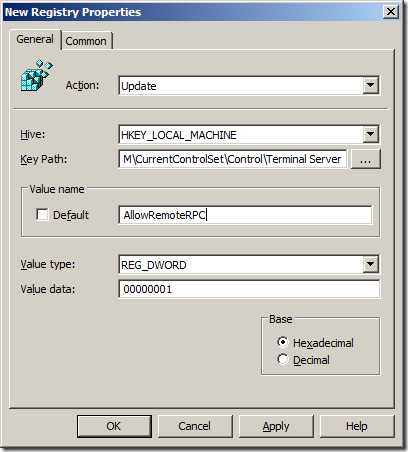
Enable Remote Procedure Call (RPC)
To enable the Remote Procedure Call (RPC) feature all we need to do is use the Group Policy Preference Registry Extension to change registry key “HKLM\SYSTEM\CurrentControlSet\Control\Terminal Server\AllowRemoteRPC†to a value of 1 (see image below).
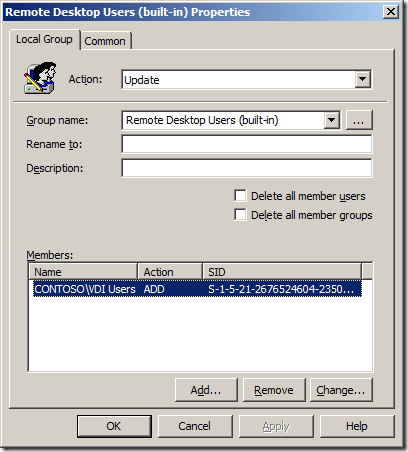
Adds selected users to the Remote Desktop Users group
You can configure the “Remote Desktop Users†group using the Group Policy Preference Local Users and Group Extension.
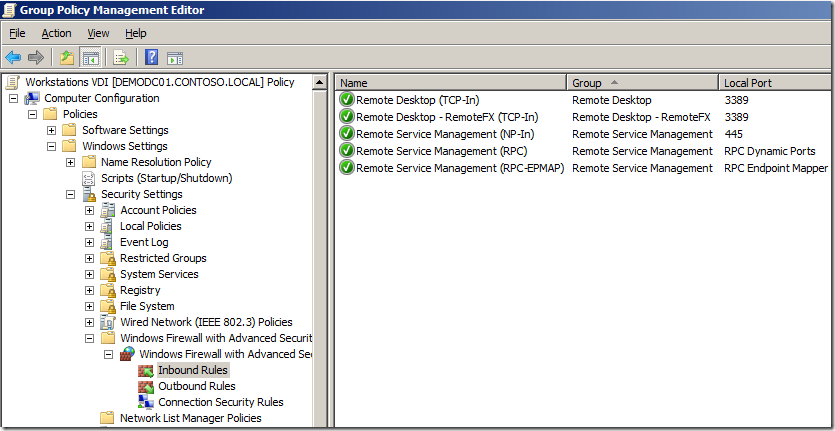
Add a Windows Firewall exception for Remote Desktop Services and Add a Windows Firewall exception for Remote Services Management
Now the two “Windows Firewall Exceptions†can be made by adding the following predefined inbound firewall exceptions under “Computer Configuration>Policies>Windows Settings>Security Settings>Windows Firewall with Advanced Securityâ€.
- Remote Desktop
- Remote Service Management
- Remote Desktop – RemoteFX (If required)
It should then look something like the image below:
The final step you need to perform on the workstation is to :
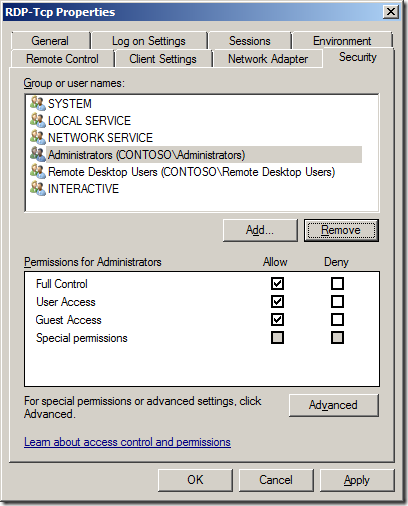
- Adds the proper RDP-TCP listener permissions for the RD Virtualization Host server
- Restarts the Remote Desktop Services service
However these steps are some what more difficult to perform as there is no Group Policy to make these configuration nor is the “Remote Desktop Session Configuration Host†tool loaded to make the changes via a GUI.
If you could load (or remotely connect this tool on Windows 7) it would look something like this by default…
So as much as a loath saying it you will need to resort to a script to perform the necessary configuration using the WMIC command.
To do this just copy the following script and put it on a server share that has the “Domain Computer†group granted read permissions.
wmic /node:localhost RDPERMISSIONS where TerminalName=”RDP-Tcp” CALL AddAccount “contoso\VDI Servers”,1
wmic /node:localhost RDACCOUNT where “(TerminalName=’RDP-Tcp’ or TerminalName=’Console’) and AccountName=’contoso\\VDI Servers'” CALL ModifyPermissions 0,1
wmic /node:localhost RDACCOUNT where “(TerminalName=’RDP-Tcp’ or TerminalName=’Console’) and AccountName=’contoso\\VDI Servers'” CALL ModifyPermissions 2,1
wmic /node:localhost RDACCOUNT where “(TerminalName=’RDP-Tcp’ or TerminalName=’Console’) and AccountName=’contoso\\VDI Servers'” CALL ModifyPermissions 9,1
shutdown /r /t 0
Note: I have used the group called “VDI Servers†so you will need to create this group and add all your VDI server to this group. This way you can use the same script to configure all your VDI workstations.
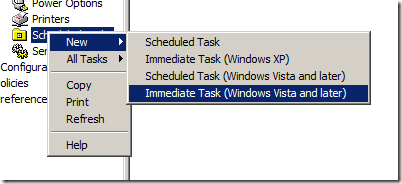
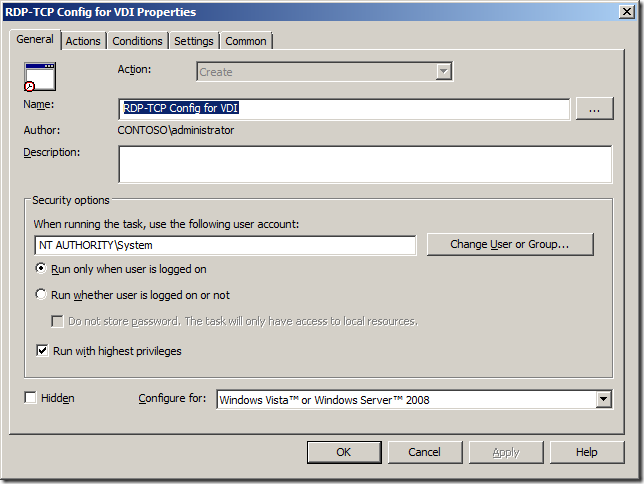
You can then call this script as a once using the “Immediate Task (Windows Vista and later)†option in the Group Policy Preferences Scheduled Task Extension
Configure the task to run as the “SYSTEM†account so it has the permission to make the required changes and reboot.
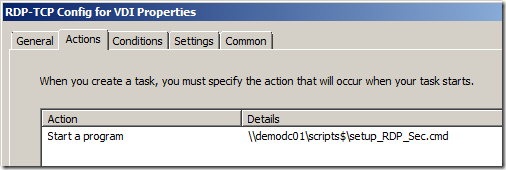
Then chose the “Start a program†action and run the script where you have saved it on the network (remember that it must have “Domain Computer†read permission granted).
You have now configured group policy to automatically configured your Windows 7 workstations as a VDI ready computer once it is placed in the VDI OU structure.
However there are still a number of other suggested configuration settings you might want to apply to this computer…




Blog Post: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/aSxvkCnV
RT @alanburchill: Blog Post: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/n22sISrJ #grouppolicy
Best Practice: Group Policy for Virtual Desktops Infrastructure #VDI #GPO http://t.co/8jJTzir7
Best Practice: Group Policy for Virtual Desktops Infrastructure #VDI #GPO http://t.co/8jJTzir7
Best Practice: Group Policy for Virtual Desktops Infrastructure #VDI #GPO http://t.co/8jJTzir7
Blog Post: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/aSxvkCnV
Best Practice: Group Policy for Virtual Desktops Infrastructure #VDI #GPO http://t.co/8jJTzir7
Blog Post: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/aSxvkCnV
Blog Post: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/aSxvkCnV
Best Practice: Group Policy for Virtual Desktops Infrastructure #VDI #GPO http://t.co/8jJTzir7
Best Practice: Group Policy for Virtual Desktops Infrastructure #VDI #GPO http://t.co/8jJTzir7
RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/ZLBvm7aT
RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/ZLBvm7aT
Will have to read QT @alanburchill: Blog Post: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rY2nQd7i
RT @stealthpuppy: RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/NDOvw20o
RT @stealthpuppy: RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/NDOvw20o
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI): http://t.co/acruNWZw
Blog Post: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/aSxvkCnV
RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/ZLBvm7aT
RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/ZLBvm7aT
RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/ZLBvm7aT
RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/ZLBvm7aT
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/placydIm
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/Sj5BhYo2
Best Practice: Group Policy for Virtual Desktops Infrastructure #VDI #GPO http://t.co/8jJTzir7
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI)
http://t.co/FlAT4TFd #vdi #gpo
RT @alanburchill Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/ZLBvm7aT
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/BzrQ6H95
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/hSfHvNE8 >Must Read
RT @xenappblog: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/LcjKYtGj >Must Read > Great Post
RT @znackattack: Best Practice: Group Policy for Virtual Desktops Infrastructure #VDI #GPO http://t.co/6Fwo5CHu
Für die Techies: RT @xenappblog: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/maF1lP7b >Must Read #VDI
Super Artikel!!! RT @AppSphere: RT @xenappblog: Best Practice: Group Policy for VDI http://t.co/EQ8V7mK1 >Must Read #VDI
Super Artikel!!! RT @AppSphere: RT @xenappblog: Best Practice: Group Policy for VDI http://t.co/zz1mK4eH >Must Read #VDI
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/hSfHvNE8 >Must Read
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) « Group Policy Center http://t.co/rjF1oDXP
Hey Alan, super awesome cool article ! Many thanks.
Alex
Group Policy for Virtual Desktops Infrastructure (#VDI) http://t.co/eNz3Gkmo by @alanburchill
@mkleef do you mind taking a look at this VDI/GPO post i wrote… http://t.co/ZUfiIlzR
Group Policy for Virtual Desktops Infrastructure (#VDI) http://t.co/eNz3Gkmo by @alanburchill
Group Policy for VDI http://t.co/sVuy9PEl
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/KCFuhj2y (via Instapaper)
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/Gqm40oWv
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI): http://t.co/NqwQeKcW
Group Policy for VDI http://t.co/sVuy9PEl
RT @JeffHicks: Group Policy for #VDI http://t.co/m4JUxJqV #VMUG
RT @JeffHicks: Group Policy for #VDI http://t.co/aobDRHMn #VMUG
"Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI)" – http://t.co/6OomSHCJ – by @alanburchill – #XenDesktop #vWorkspace
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/legcdxeF
"Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI)" – http://t.co/6OomSHCJ – by @alanburchill – #XenDesktop #vWorkspace
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
“@andreleibovici: Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/nlgJ78e7†uff, cuanto que aprender…
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/rIwerwKh < awesome resource in request by @thesanzone
Best Practice: Group Policy for Virtual Desktops Infrastructure (VDI) http://t.co/Gz2geQqH via @alanburchill
Havs anyone heard of a way to collect the user profile without installing a agent on the end users machines?
Best article about virtual desktop and group policy best pracice I came across on the internet….
great article
Need help with a group policy IE 11not saving passwords Load balances servers
roaming profiles on R2012 R2 , only saves on the first one it was created. any help much appreciated